
An insider threat is typically an employee or contractor who has authorized access to your organization’s critical systems or the data and poses a security risk to the organization by misusing the authorized access.
The insider doesn’t necessarily have to be a current employee or stakeholder. They can be either a former employee or board member who still has access to your organization’s proprietary or sensitive information.
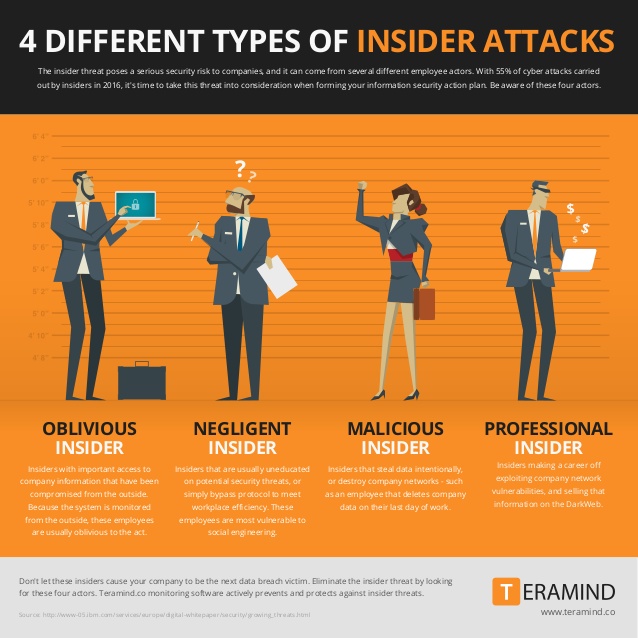
As you can see in the image bellow there are a number of different types of attacks an insider can launch.
Over the years, TBG Security has developed a methodology for identifying insider threats to your organization.
An insider threat assessment addresses threats posed by trusted individuals and assets. Whether it’s a rogue employee, a nefarious contractor or an honest user who has fallen prey to a sophisticated phishing or malware attacks this service looks at weaknesses and malicious opportunity from the perspective of a user who already has access within the environment.
Insider Threat assessments are designed to test security controls already in place, to test the rigor of security configurations, identify areas of lax access controls, and to test the defensive mechanisms in place to spot and respond to abuses.
During the Insider Threat Assessment, a senior TBG security engineer will be onboarded just as if they were being given a position within the company and the organization will provide a corporate issued laptop. The TBG security engineer will be provided a user profile similar to that of a “standard” user within the company. The goal will be to take on the user identity and attempt to exfiltrate data and escalate rights both on the laptop itself and within and around the network and services to which the user has been granted access.
The Insider Threat Threat Assessment service will cover:

