
With many security companies pushing out their threat predictions for 2016, we thought it best to review as many as we could in order to compile a definitive list of what to look out for in this coming year.
And, as independent consultants without any direct or indirect ties to specific security providers, we are well placed to provide an product-agnostic perspective on the state of security in 2016.
More importantly, we wanted to give you expert advice on how you can protect against tomorrow threats without breaking your IT security budget.
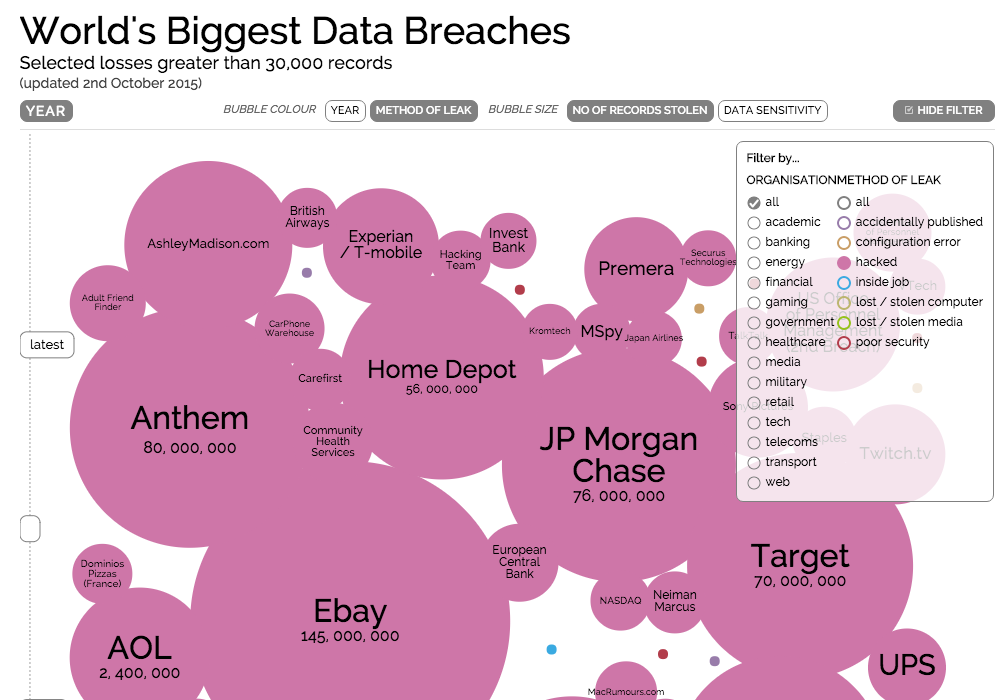
Sadly, we expect more of the same when it comes to massive data breaches. This World’s Biggest Data Breaches’ image displays many of the major data breaches of 2015. When organized by ‘method of leak’, you can quickly see that many are a result of unauthorized access.
While we expect the number of public data breaches to intensify, we also expect to see DDoS attacks continue to dominate the news. In 2015, one of the more notorious DDoS attacks and subsequent data breach of almost 160,000 customer records stemmed from UK telecoms provider TalkTalk.
The TalkTalk data breach “turned out to be the biggest British cyber attack on record, costing the firm an estimated £35 million,” according to the Information Age.
“It’s vital that all businesses pay attention and learn from these previous breaches. No company wants to have their name in lights along with the words ‘massive data breach’. Our job is to make sure that everything on a network is carefully tested to withstand the most relentless attacks,” said Kevin Gorsline, Vice President of Compliance Services at TBG Security,” said Kevin Gorsline, Vice President of Compliance Services at TBG Security.
Allianz reported late last year that the global cyber insurance market is predicted to grow to more than $20 billion by 2025. The top five countries in term of cybercrime costs are the US, China, Japan, Germany and France.
And U.S. insurers have massively increased their premiums, ”leaving firms that are perceived to be high risk scrambling for cover,” reported Newsman.
Deductibles are also being increased, but coverage in some cases is being capped at $100 million, leaving larger corporations exposed to losses that can far surpass the cover.
A Ratheon/Websense press release, entitled Raytheon|Websense Predicts 2016 Cybersecurity Threat Landscap, reported:
“Insurance companies will mature their offerings with qualifications, exceptions and exemptions allowing them to refuse payment for breaches caused by ineffective security practices, while premiums and payouts will become more aligned with underlying security postures and better models of the cost of an actual breach. Further, insurance companies will greatly affect security programs, as requirements for insurance become as significant as many regulatory requirements (PCI, HIPAA, ISO 27001).”
Businesses would be wise to reduce their security risk exposure in terms of their security implementations and configurations. Strengthening internal security training procedures will also help to reduce the risk of a breach, not to mention insurance premiums.
Compliance reviews, penetration testing and training are all available from the infosecurity experts at TBG Security.
The onslaught of internet-connected systems and devices opens more doors for hackers to penetrate businesses.
Gartner forecasted in November that a whopping 6.4 billion connected things will be in use worldwide in 2016, up 30 percent from 2015, reaching 20.8 billion by 2020. This year, 5.5 million new things will get connected every day.
The “..Internet of Things (IoT) will support total services spending of $235 billion in 2016, up 22 percent from 2015. Services are dominated by the professional category (in which businesses contract with external providers in order to design, install and operate IoT systems), however connectivity services (through communications service providers) and consumer services will grow at a faster pace,” Gartner reported.
The major concern with the onslaught of IoT is the impact on security implications.
“Cyber attacks have historically caused little physical damage, but the proliferation of IoT will enable more disruption and actual physical damage instead of just virtual hardware and software disruption,” says McAfee’s 2016 prediction report.
“New connectivity means a broader attack surface for hackers to steal personally identifiable information (PII), medical records, and intellectual property. IoT security requires a myriad of security layers which can be challenging for most organizations to implement. Regular penetration testing to insure appropriate security is in place is one way to stay ahead of hackers and determine an organizations level of readiness,” continued Kevin Gorsline, Vice President of Compliance Services at TBG Security.
TBG Security is a leading provider of information security and risk management solutions for Fortune 100 and Fortune 500 companies. TBG designs and delivers cyber security solutions to work in harmony with existing operations. Companies depend on TBG services in areas including risk management, penetration testing, security policy development, security strategies for compliance, business continuity, network security, managed services, software and service integration and incident response.
For more information on how TBG Security can help your organization with your information security initiatives please visit https://tbgsecurity.com.